
Everything these days is digital, including banking, food delivery, and just about everything else we use. Many applications collect sensitive information about their users, such as their address, credit card number, and other personally identifiable information (PII). Because they hold a large amount of data, hackers are constantly on the lookout for ways to gain access to such applications to steal important information from their users. Thus, it is critical that the application's security is properly addressed.
The application security process is carried out to shore up the security posture of the entire program as well as the user data to keep it safe from attackers.
Different Forms of Application Security (News - Alert)
To strengthen the security of both users and apps, different types of application security can be implemented.
Application Security Testing
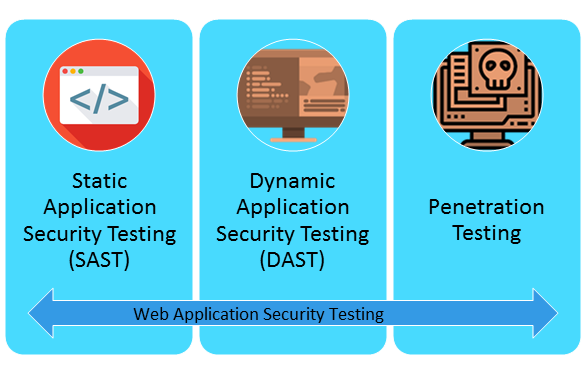
Application security testing can be divided into two categories: static application security testing and dynamic application security testing. Both of these tests are performed during the software development lifecycle (SDLC) before the application is deployed, allowing any vulnerabilities that may exist in the application to be patched before the application is deployed.
One tests the application's source code in its entirety, while the other does a vulnerability assessment when the application or software is in the final stages of deployment. As a result, if any vulnerabilities are discovered, they will be addressed prior to deployment.
Authentication
Authentication ensures that only users with valid credentials can gain access to the application through identification and authentication. However, due to the increased attack surface of applications, usernames and passwords have been replaced with usernames and one-time passwords (OTP). As a result, passwords and other accounts of users are not compromised, and other accounts of users can be safely used.
Essentially, authentication is being carried out to identify the person who is attempting to access the resources on the network.
Authorization


It is used to ensure that users only access info that is relevant to them or to which they have permission to gain access. If authorizations are correctly enforced, the attack surfaces are reduced, and since users cannot edit information to which they do not have access, the situation cannot progress to data disclosure or breach. As a result, it ensures that users can only access data to which they have been granted access permission.
Encryption
Encryption is used to protect data from being intercepted by a malicious third party (MiTM) attack and in the event that the organization's servers have been compromised.
It converts plaintext into a form that humans cannot read. This also prevents sensitive information from being stolen by attackers and ensures that user data is protected. Data should be encrypted both in transit and at rest to ensure that no user information is leaked or otherwise compromised.
Logging
All of the tasks or transactions being carried out should be recorded in some manner. It assists in the identification of unsecured or unauthorized network access points. The file contains the data of all high-value transactions, such as login and logout, and they are kept safe and secure.
Different types of properties are contained within it, such as users’ IP addresses, the endpoint they access, and the data being sent. Then, the logs can be examined to see if any data has been accessed by unauthorized users or if any vulnerabilities have been taken advantage of.
Conclusion
The usage of application security is becoming more widespread. There are several types of popular application security methods. Every application requires tools that can perform static application security testing so that any vulnerabilities can be identified and patched as soon as possible during the development process.
Since data is encrypted, there is a probability that the attacker will not be able to decrypt it once it has been delivered. Encryption is usually used to protect applications when they are deployed and to protect data during breaches.




